Information Security Objectives
Taxonomies for Information Security Objectives from various sources.
Handbook of Applied Cryptography
From Handbook of Applied Cryptography Menezes et al https://cacr.uwaterloo.ca/hac/, page 3
privacy or confidentiality
keeping information secret from all but those who are authorized to see it.
data integrity
ensuring information has not been altered by unauthorized or unknown means.
entity authentication or identification
corroboration of the identity of an entity (e.g., a person, a computer terminal, a credit card, etc.).
message authentication
corroborating the source of information; also known as data origin authentication.
signature
a means to bind information to an entity.
authorization
conveyance, to another entity, of official sanction to do or be something.
validation
a means to provide timeliness of authorization to use or manipulate information or resources.
access control
restricting access to resources to privileged entities.
certification
endorsement of information by a trusted entity.
timestamping
recording the time of creation or existence of information.
witnessing
verifying the creation or existence of information by an entity other than the creator.
receipt
acknowledgement that information has been received.
confirmation
acknowledgement that services have been provided.
ownership
a means to provide an entity with the legal right to use or transfer a resource to others.
anonymity
concealing the identity of an entity involved in some process.
non-repudiation
preventing the denial of previous commitments or actions.
revocation
retraction of certification or authorization
Four Goal framework
Of the goals above, the following four are fundamental, others are derived from them:
Confidentiality is a service used to keep the content of information from all but those authorized to have it. Secrecy is a term synonymous with confidentiality and privacy. There are numerous approaches to providing confidentiality, ranging from physical protection to mathematical algorithms which render data unintelligible.
Data integrity is a service which addresses the unauthorized alteration of data. To assure data integrity, one must have the ability to detect data manipulation by unauthorized parties. Data manipulation includes such things as insertion, deletion, and substitution.
Authentication is a service related to identification. This function applies to both entities and information itself. Two parties entering into a communication should identify each other. Information delivered over a channel should be authenticated as to origin, date of origin, data content, time sent, etc. For these reasons this aspect of cryptography is usually subdivided into two major classes: entity authentication and data origin authentication. Data origin authentication implicitly provides data integrity (for if a message is modified, the source has changed).
Non-repudiation is a service which prevents an entity from denying previous commitments or actions. When disputes arise due to an entity denying that certain actions were taken, a means to resolve the situation is necessary. For example, one entity may authorize the purchase of property by another entity and later deny such authorization was granted. A procedure involving a trusted third party is needed to resolve the dispute.
Everyday Cryptography
From Everyday Cryptography Martin, OUP, p. 12
Confidentiality is the assurance that data cannot be viewed by an unauthorised user.
Data Integrity is the assurance that data has not been altered in an unauthorised (which includes accidental) manner. This assurance applies from the time the data was last created, transmitted, or stored by an authorised user. Data integrity is not concerned with the prevention of alteration of data, but provides a means for detecting whether data has been manipulated in an unauthorised way.
Data origin authentication is the assurance that a given entity was the original source of received data. In other words, if a technique provides data origin authentication that some data came from Alice, then this means that the receiver, Bob, can be sure that the data did originally come from Alice at some time in the past. It doesn’t guarantee the immediate source of the data, or the time, just that it originally came from a named source. For this reason data origin authentication is sometimes referred to message authentication, since it is primarily concerned with the authentication of the data (message) not the immediate interlocutor.
Non-repudiation is the assurance that an entity cannot deny a previous commitment or action. Most commonly, non-repudiation is the assurance that the original source of the data cannot deny to a third party that this is the case. Note that this is a stronger requirement than data origin authentication, since data origin authentication only requires this assurance to be provided to the receiver of the data. This service is most desirable in situations where there is potential for dispute to arise over the exchange of data.
Entity authentication is the assurance that a given entity is involved and currently active in a communication session. If a technique provides entity authentication of Alice then this means that by applying it we can be sure that Alice is engaging with us now. It requires the adoption of a freshness mechanism. This can be referred to as identification since it is concerned with who am I communicating with now?
Note the following properties (p. 14)
Data origin authentication is stronger than data integrity. If we have the former we must have the latter, but not vice versa.
Non-repudiation of a source is stronger than data origin authentication. Non-repudiation cannot be provided without data origin authentication. Requires the binding of source and data to be verifiable by a third party.
Data origin authentication and entity authentication are different. Entity authentication is the service required when accessing resources. Data origin authentication is useful in situations where one entity is forwarding information on behalf of another.
Data origin authentication plus freshness check can provide entity authentication.
ISO Standards
As described in Dent and Mitchell, User’s Guide to Cryptography and Standards, ch. 1, p 22ff.
ISO developed a seven part ‘security frameworks’ standard to cover the main services:
ISO/IEC 10181-1 (1996): Overview;
ISO/IEC 10181-2 (1996): Authentication framework;
ISO/IEC 10181-3 (1996): Access control framework;
ISO/IEC 10181-4 (1997): Non-repudiation framework;
ISO/IEC 10181-5 (1996): Confidentiality framework;
ISO/IEC 10181-6 (1996): Integrity framework;
ISO/IEC 10181-7 (1996): Security audit and alarms framework
Followed from ISO 7498-2, the pioneering security standard.
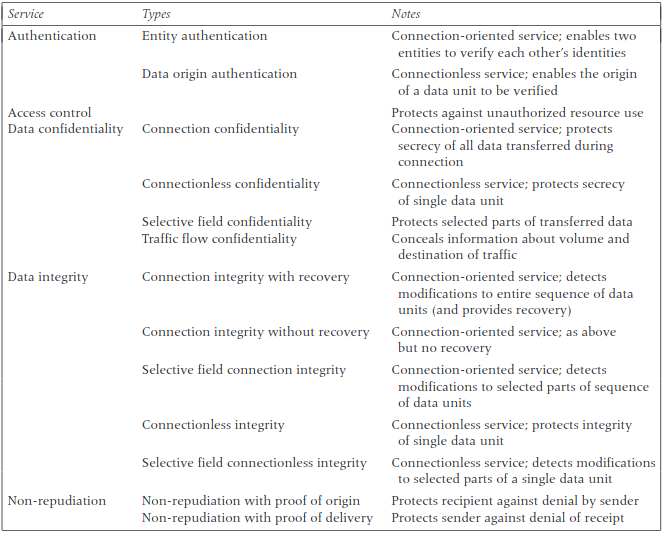
ISO 7498-2 defines five main categories of security service:
Authentication, which can be subdivided into entity authentication, the corroboration that the entity at the other end of a communications link is the one claimed, and data origin authentication, the corroboration that the source of data received is as claimed;
Access control (i.e., the prevention of unauthorized use of a resource).
Data confidentiality (i.e., the prevention of the disclosure of data to unauthorized entities);
Data integrity (i.e., the prevention of unauthorized alteration or destruction of data by an unauthorized entity);
Non-repudiation (i.e., the prevention of denial by an entity that it has taken a particular action, such as sending or receiving a message).
Authentication
Entity authentication (or “peer entity authentication” as it is referred to in ISO 7498-2) provides corroboration to one entity that another entity is as claimed. This service may be used at the establishment of (or during) a communications connection to confirm the identities of one or more of the connected entities. This service provides confidence, at the time of use only, that an entity is not attempting to impersonate another entity or that the current communications session is an unauthorized replay of a previous connection.
Data origin authentication provides corroboration to an entity that the source of received data is as claimed. However, it does not, in itself, provide protection against duplication or modification of data. These latter properties are issues addressed by a data integrity service. Of course, in practice, data integrity and data origin authentication are usually provided using the same mechanism.
Access control
The access control service provides protection against the unauthorized use of resources. This protection may be applied to a variety of types of access and resources, such as the following:
The use of a communications resource for the transmission of data;
The reading, writing, or deletion of an information resource;
The use of a processing resource to execute programs.
Data confidentiality
ISO 7498-2 defines four types of data confidentiality service; all these services provide for the protection of data against unauthorized disclosure. The four types are listed as follows:
Connection confidentiality, which provides for the confidentiality of all user data transferred using a connection;
Connectionless confidentiality, which provides for the confidentiality of all user data transferred in a single connectionless data unit (i.e., a data packet);
Selective field confidentiality, which provides for the confidentiality of selected fields within user data transferred in either a connection or a single connectionless data unit;
Traffic flow confidentiality, which provides for the confidentiality of information that might be derived from observation of traffic flows (e.g., the time at which data is sent, the volumes of data sent to or received by particular recipients, or the length of individual messages).
Data integrity
ISO 7498-2 defines five types of data integrity service; all these services counter active threats to the validity of transferred data. The five types are described as follows.
- Connection integrity with recovery: This service provides integrity protection for all the user data transferred using a connection and detects any modification, insertion, deletion, or replay of data within an entire data unit sequence. The term with recovery means that if some form
of modification is detected, then the service attempts to recover the correct data, typically by requesting that the data be resent.
Connection integrity without recovery: As previously but with no recovery attempted if an integrity failure is detected.
Selective field connection integrity: This service provides integrity protection for selected fields within the user data or within a data unit transferred over a connection.
Connectionless integrity: This service provides integrity assurance to the recipient of a data unit. More specifically, it enables the recipient of a connectionless data unit to determine whether that data unit has been modified. Additionally, a limited form of replay detection may
be provided.
- Selective field connectionless integrity: This service provides integrity protection for selective fields within a single connectionless data unit.
Non-repudiation
ISO 7498-2 defines two types of non-repudiation service.
Non-repudiation with proof of origin: The recipient of data is provided with evidence of the origin of data. This will protect against any subsequent attempt by the sender to falsely deny sending the data. This service is usually abbreviated to non-repudiation of origin.
Non-repudiation with proof of delivery: The sender of data is provided with evidence of delivery of data. This will protect against any subsequent attempt by the recipient to falsely deny receiving the data. This service is usually abbreviated to non-repudiation of delivery.
In both cases the evidence provided by the service must be of value in helping to resolve disputes using a trusted third party acting as an arbiter (e.g., a judge in a court of law). This means that, in the case of non-repudiation of origin, it must not be possible for evidence to be fabricated by the recipient, since otherwise the evidence will be of no value in dispute resolution. Similarly the evidence generated by a non-repudiation of delivery service must not be readily fabricated by the data sender or any party other than the recipient.
Summary